Introduction
Fake banking sites aren’t just a customer problem. CFPB guidance makes clear that when a fraudster obtains account access information through deception and uses it to initiate a covered EFT, the transfer may qualify as an unauthorized EFT under Regulation E. That means cloned login pages can create investigation obligations, provisional credit requirements, and reimbursement exposure for banks, even when the customer typed the password themselves.
That is the compliance reality many financial institutions are still underprepared for. When deception is the mechanism, the “customer authorized the login” defense becomes much harder to sustain. Banks need evidence that shows how access was obtained, how the transfer was initiated, and whether the claim falls within Regulation E’s unauthorized EFT framework.
Fake-site fraud becomes a bank-side liability problem when stolen credentials move from impersonation exposure into unauthorized account access, making account takeover fraud a compliance issue as much as a fraud issue.
This guide covers what the updated regulatory framework actually requires, where transaction monitoring falls short, and what a defensible compliance posture looks like when fake-site fraud is the attack vector.
Introduction: Why Regulation E Is Now a Digital Fraud Problem
A customer calls your fraud line to dispute a $4,200 electronic transfer they say they never authorized. Your investigation reveals they entered credentials on a pixel-perfect clone of your bank’s login page, reached via a phishing email. They believed they were logging into their account. They weren’t.
Under the old mental model, many banks argued the customer “authorized” the login. That argument is losing ground fast.
The FTC reported that US consumers lost $2.088 billion to fraudulent bank transfers and payments in 2024. Behind a significant share of those losses sits a fraud chain that starts not inside your systems, but on a fake site your customer had no way to identify as fraudulent. Regulators, courts, and financial institutions are paying closer attention to how fraudulently obtained access information affects reimbursement obligations. The New York v. Citibank litigation also shows why this area must be handled carefully: the CFPB later withdrew its filing in that case, making wire-transfer coverage under EFTA and Regulation E a contested issue rather than a settled point.
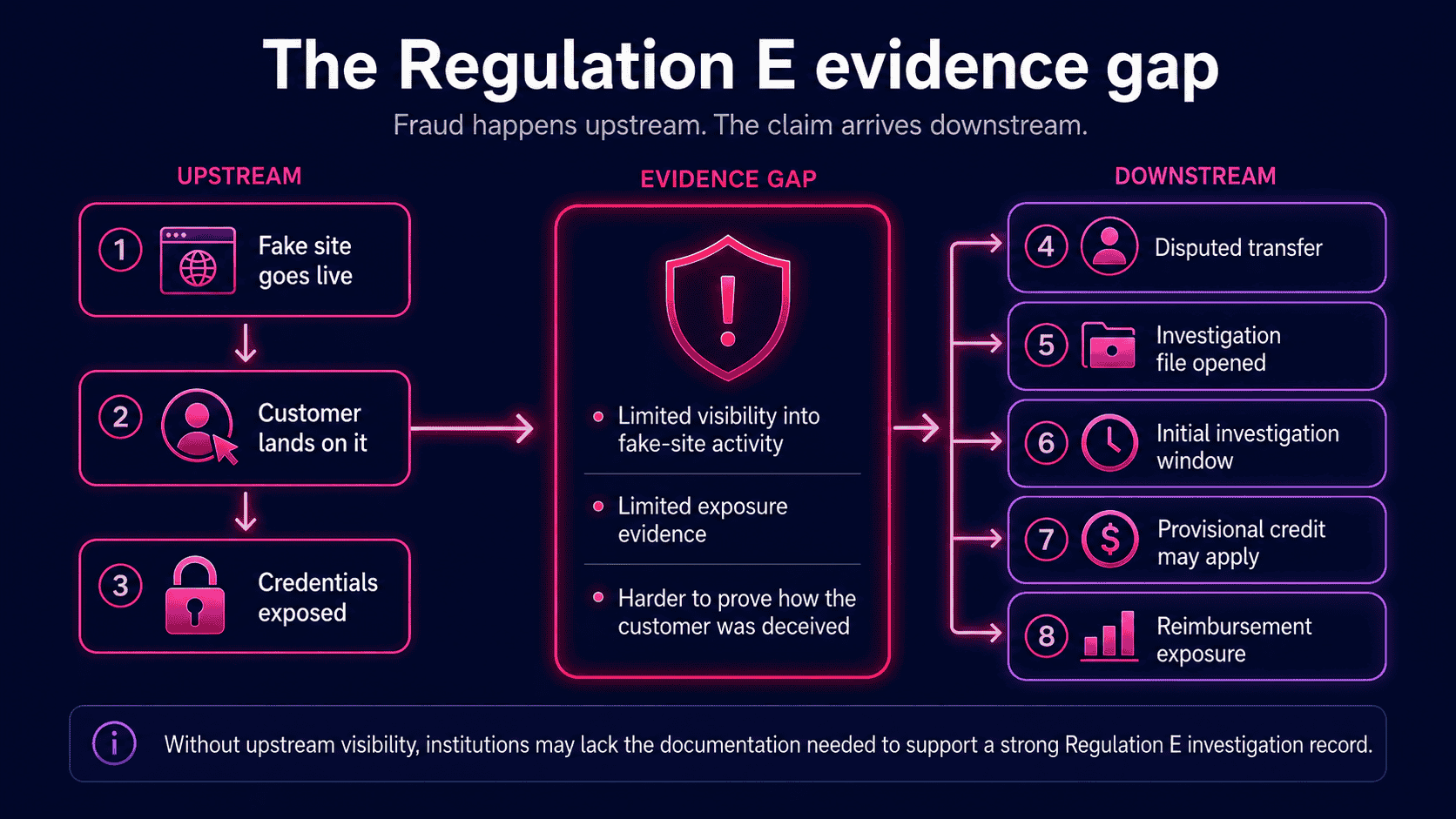
The core tension is timing. Regulation E claims are handled after a disputed transfer, but the evidence needed to evaluate those claims often sits upstream, at the point where credentials were obtained through deception.
This guide covers the legal framework, the fraud chain, the compliance gap most banks are missing, and what a defensible posture looks like in practice.
Regulation E Liability in the Digital Banking Era: What’s Changed
Most banks know Regulation E. Fewer understand how much its liability calculus has shifted in the past 18 months.
The Electronic Fund Transfer Act (EFTA), codified at 15 U.S.C. § 1693 et seq. and implemented through the CFPB’s Regulation E (12 CFR Part 1005), establishes the baseline consumer protection framework for electronic fund transfers. At its core is a deceptively simple definition: an “unauthorized electronic fund transfer” under 15 U.S.C. § 1693a(12) is any EFT initiated by a person other than the consumer without actual authority to initiate the transfer, and from which the consumer receives no benefit.
Consumer liability caps are tiered and time-sensitive:
- $50 maximum if the consumer reports the loss within two business days of learning of it
- Up to $500 if reported between two and 60 days after statement delivery
- Unlimited liability if the consumer fails to report within 60 days of the statement date
On the institution’s side, 12 CFR § 1005.11 sets the investigation clock. A financial institution has 10 business days to resolve an error notice. If it can’t, it must provisionally credit the disputed amount and has up to 45 days total to complete its investigation. Miss either deadline, and the institution faces automatic liability for the disputed amount plus damages.
That framework was written for a world of lost debit cards and stolen PINs. Digital impersonation attacks broke it.
- The CFPB guidance that matters for stolen-credential fraud
The CFPB’s Electronic Fund Transfers FAQs directly address a question banks face in stolen-credential cases: when a fraudster obtains account access information through deception and uses it to initiate a covered EFT, should the resulting transfer be treated as authorized or unauthorized?
The Bureau’s guidance is clear on the core principle: when a third party fraudulently obtains a consumer’s account access information and uses it to initiate a covered EFT, the transfer can qualify as an unauthorized EFT under Regulation E. The FAQs identified two scenarios now classified as unauthorized:
- A third party calls the consumer, impersonates a bank representative, and tricks the consumer into providing login credentials or one-time passcodes.
- A third party uses phishing or other methods to access a consumer’s computer and observe account login information being entered.
The legal significance is precise. The EFTA’s existing exclusion for transfers initiated by “a person who was furnished the access device” does not apply when that access was obtained through fraud. The consumer’s act of typing credentials into what they believed was a legitimate site does not constitute “actual authority” granted to the fraudster.
The “authorized vs. unauthorized” distinction no longer turns on who pressed the keys. It turns on whether the third party obtained access through deception.
One important clarification: separate CFPB activity around EFTA and emerging payment mechanisms should not be conflated with the stolen-credential guidance. For this article, the relevant point is narrower: fraudulently obtained account access information can affect whether a subsequent covered EFT is treated as unauthorized under Regulation E.
For compliance and fraud teams, the practical implication is direct: fraud chains that begin with consumers being deceived into submitting credentials can create Regulation E investigation, provisional credit, and reimbursement exposure when those credentials are later used to initiate covered electronic transfers. The institution bears the investigation burden and may face provisional credit obligations, reimbursement exposure, and documentation scrutiny.
The ‘Authorized vs. Unauthorized’ Distinction Under Deception Attacks
The traditional bank defense in credential-theft cases has been blunt: the consumer used their own login, so the transfer was authorized. That defense is much harder to sustain when access was obtained through deception.
Under the EFTA, an unauthorized EFT is a transfer “from a consumer’s account initiated by a person other than the consumer without actual authority to initiate the transfer.” The operative word is actual authority. Actual authority can’t exist when it was obtained through fraudulent misrepresentation.
The CFPB’s FAQ guidance makes this explicit. When a consumer is fraudulently induced into sharing account access information, and a third party uses that information to initiate an EFT, the CFPB confirms the transfer is an unauthorized EFT under Regulation E. The consumer’s act of entering credentials on what they believed was a legitimate banking site does not constitute “furnishing” an access device. Deception can undermine the argument that the fraudster had actual authority.
The legal reasoning mirrors contract law’s fraud-in-the-inducement doctrine: consent obtained through misrepresentation isn’t valid consent. A customer who types their password into a cloned banking site is not intentionally authorizing a fraudster to initiate a transfer. The institution still needs to determine how access was obtained and whether the resulting transfer qualifies as unauthorized under Regulation E.
Banks can no longer summarily deny claims on the basis that the consumer “gave” their credentials to the fraudster. As Thompson Coburn noted in its analysis of the CFPB FAQ guidance, financial institutions can’t rely on prior commentary to deny these claims outright. The investigation must assess whether deception was the mechanism by which access was obtained.
The CFPB has also confirmed that consumer negligence can’t be used to impose liability beyond what Regulation E permits. Even if a customer failed to spot a convincing fake site, that failure doesn’t shift the loss back to them.
The burden sits with the institution: investigate the deception vector, not just the transaction.
Dispute Resolution Timelines and Documentation Requirements
The clock starts the moment a consumer files a Regulation E claim. In fake-site fraud cases, most banks are already behind.
Under 12 CFR § 1005.11, the mechanics are precise:
- Generally 10 business days to investigate and determine whether an error occurred, with certain new-account transactions allowed up to 20 business days
- Up to 45 days to complete an extended investigation when provisional credit is provided, or up to 90 days for certain transactions
- Written explanation required within three business days of completing the investigation if the bank determines no error occurred
That written explanation is where fake-site fraud cases get painful.
To deny a claim, a bank must explain why the transaction was authorized. In a standard fraud scenario, that’s straightforward: review device fingerprints, IP addresses, and behavioral signals. But when a customer was deceived by a cloned banking site, the bank’s internal logs show a clean login. The credentials matched. The session looked normal. The fraud happened upstream, on infrastructure the bank never saw.
The bank can’t explain what it doesn’t know exists.
This creates a compounding documentation problem. Regulation E investigations require banks to maintain records of their methodology, the evidence reviewed, and the basis for their determination. In fake-site cases, a defensible investigation record needs to include:
- Evidence that the fraudulent site existed and was active during the relevant period
- Data on how customers were directed to it (phishing email, SEO poisoning, malicious ad)
- Confirmation of which credentials were harvested and when
Most banks have none of this. No record of the fake site’s deployment, no timeline of its activity, no way to identify which customers were exposed before the fraud completed. That’s not just an investigation gap. It’s a compliance gap that examiners will find, and that plaintiffs’ attorneys will exploit.
Ultimately, the documentation you can’t produce is the liability you can’t defend.
How Fake Banking Sites Create Regulation E Exposure
Fake banking site fraud doesn’t happen in one dramatic moment. It unfolds across five distinct steps, each one moving the liability clock closer to the bank.
- Step 1: Site deployment
A fraudster registers a domain that closely mimics a bank’s legitimate URL, using typosquatting, homograph characters, or subdomain manipulation. They deploy a pixel-perfect clone of the bank’s login page. These sites can be live within hours of domain registration, long before any takedown request reaches a registrar.
- Step 2: Customer acquisition
The fraudster drives traffic to the fake site through phishing emails, smishing, SEO poisoning, or paid social media ads. SEO poisoning is particularly insidious: the fake site appears above the legitimate one in branded search results, so a customer who types the bank’s name into Google may click the fraudulent link first. Financial institutions are the most impersonated sector in phishing attacks, according to the APWG’s 2024 Phishing Activity Trends Report, with banking and payment services making up a disproportionate share of all credential-harvesting sites detected.
- Step 3: Credential harvesting
The customer, believing they’re on the legitimate banking site, enters their username, password, and sometimes their MFA code. The fake site captures all of it in real time. To avoid raising suspicion, many fake sites display a fake error message and redirect the customer to the real site. The victim has no idea anything went wrong.
- Step 4: Transfer initiation
The fraudster uses the harvested credentials to log into the legitimate banking portal and initiates covered electronic transfers, such as ACH payments, debit transactions, or certain P2P payments. The window between credential capture and fraudulent transfer can be minutes. By the time the customer notices an alert, the funds are often already gone.
- Step 5: The Regulation E trigger
The customer files a dispute. Under the CFPB’s updated guidance, this qualifies as an unauthorized electronic fund transfer, regardless of the fact that the customer typed in their own credentials. The bank is now on the clock: provisional credit must be issued, an investigation must be opened, and documentation must be maintained.
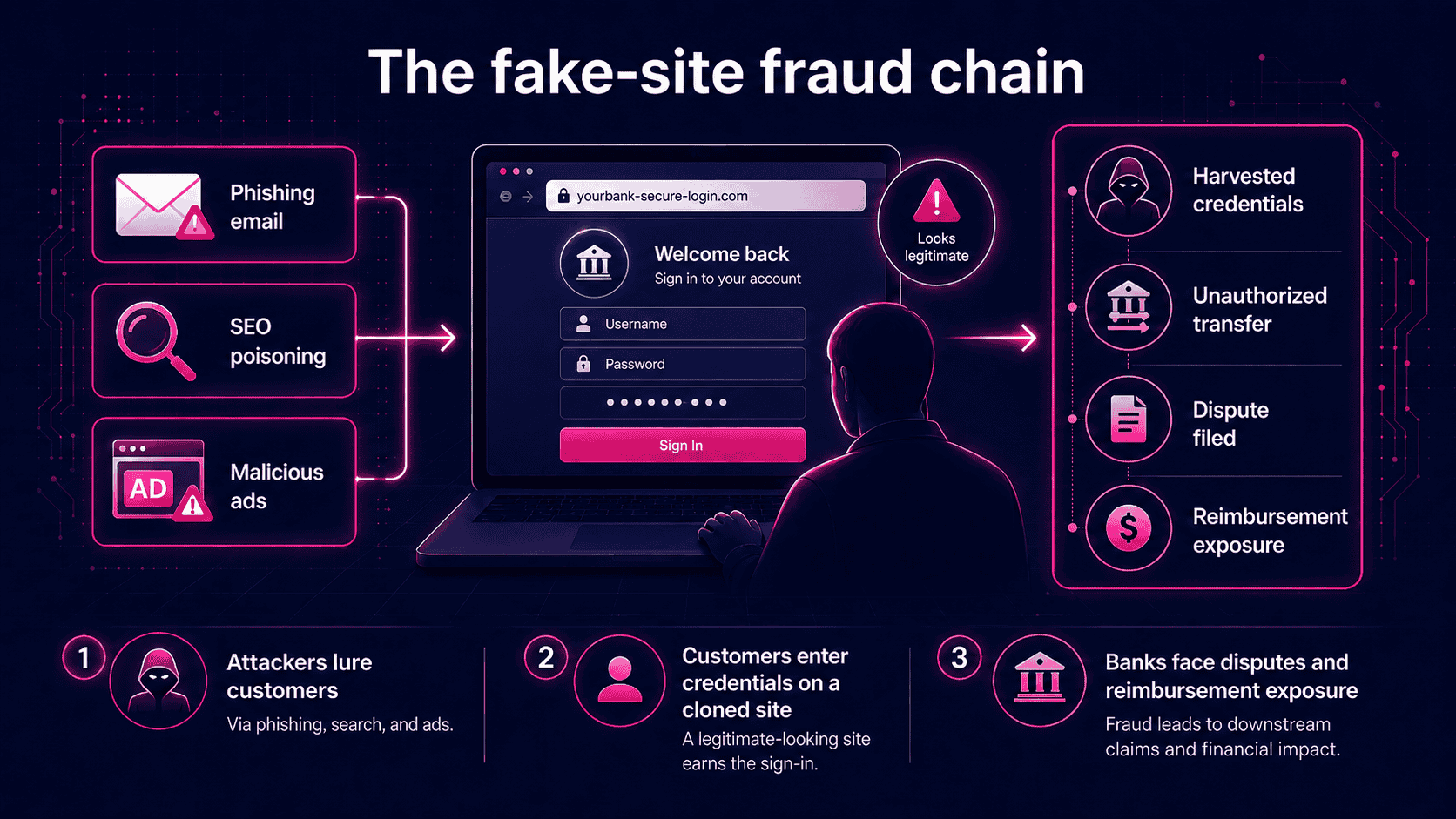
The financial exposure is not theoretical. The FTC reported that imposter scams resulted in $2.95 billion in consumer losses in 2024, with bank transfers being the highest-loss payment method of any fraud category. The FBI IC3’s 2024 Internet Crime Report recorded 193,407 phishing and spoofing complaints in 2024 alone, with total cybercrime losses exceeding $16.6 billion.
Here’s the kicker: every dispute involving a fake banking site is now a potential Regulation E liability event for the institution. The fraud chain starts at the fake site. Most banks’ controls don’t start until Step 4, when the fraudulent transfer is already in motion.
Who Bears the Loss: Liability Allocation in Practice
Here’s the uncomfortable default: when a fake-site fraud claim lands on a compliance officer’s desk, the institution may face significant reimbursement exposure unless its investigation supports a defensible determination.
Under Regulation E banking rules, the burden of proof sits with the financial institution. If the bank can’t show the consumer authorized the transfer with genuine, uncoerced intent, the transaction is unauthorized. Deception-induced credentials don’t count as real authorization. The consumer typed their details believing they were on your site. They weren’t. That’s the bank’s problem now.
The negligence carve-out makes this worse. Regulation E explicitly prohibits using consumer negligence as grounds for imposing liability beyond the statutory caps. Even if a customer clicked an obvious phishing link or ignored browser warnings, the bank can’t shift losses beyond $50 or $500 depending on the reporting window. Consumer behavior that might constitute negligence under state law is simply irrelevant under the federal framework.
In practice, most fake-site victims report within the statutory windows. They spot the unauthorized transfer fast. That means the bank faces full reimbursement exposure in the majority of cases.
The aggregate math is brutal. A single phishing campaign targeting 10,000 customers with a 2% conversion rate and an average account loss of $3,000 produces $600,000 in direct reimbursement exposure. That’s before a single investigator opens a case file.
Here’s the kicker: direct reimbursement is only the starting point. According to the LexisNexis True Cost of Fraud Study 2025, every $1 of fraud loss now costs North American financial institutions $5.75 in total costs when investigation, remediation, compliance overhead, and operational burden are factored in. That $600,000 reimbursement exposure becomes a $3.45 million operational hit.
The statutory caps protect consumers. They don’t protect banks.
The Compliance Gap Most Banks Aren’t Addressing
Most mid-to-large financial institutions have built serious fraud control stacks. Transaction monitoring, behavioral analytics, device fingerprinting, MFA, fraud scoring models. The investment is real. Here’s the problem: every single one of those controls activates after the customer has already been deceived.
None of them touch the fake banking site where the deception actually begins.
Think of it like a bank branch with an excellent vault, motion sensors, and armed guards, but no lock on the front door. By the time a fraudster walks out with valid credentials, downstream controls are playing catch-up against someone who already holds the keys. The fraud event didn’t start at login. It started the moment a customer landed on a cloned site and typed in their username.
- The numbers make the exposure hard to ignore.
Javelin Strategy & Research found that account takeover fraud resulted in nearly $13 billion in losses in 2023 alone, up 15% from the prior year. The APWG Phishing Activity Trends Report for Q1 2025 confirmed attacks against the online payment and banking sectors grew, together accounting for 30.9% of all phishing attacks that quarter. The FTC’s 2024 fraud data shows US consumers lost $12.5 billion to fraud, with imposter scams ranking as the second-highest loss category.
According to TransUnion’s H2 2025 Global Fraud Report, account takeover fraud accounts for nearly one-third (31%) of all reported fraud losses in the US. That’s not a niche threat. That’s the dominant fraud vector hitting financial institutions right now.
- Reactive controls don’t stop this. They document it.
Transaction monitoring flags suspicious transfers after credentials are used. Post-login behavioral analysis catches anomalies after authentication succeeds. Fraud scoring models assign risk scores after the session is already live. Each tool generates investigation workload, provisional credit obligations, and reimbursement costs. They’re essential, but they’re operating in the wrong part of the attack timeline.
Upstream controls work differently. Fake site detection and real-time disruption prevent the credential harvest from occurring at all. Fewer exposed credentials means fewer downstream events for fraud, compliance, and investigation teams to manage.
The automation gap makes this worse. The LexisNexis True Cost of Fraud Study 2025 found that 44% of North American financial institutions primarily rely on manual processes, creating significant lag in fraud response. Manual workflows can’t match the speed at which fake sites are deployed and credential harvests occur, often within hours of a phishing campaign launching.
The compliance implication is direct. Under the CFPB’s updated Regulation E guidance, a bank with no controls at the fake-site layer has no documented evidence it took reasonable steps to prevent the deception that triggered the unauthorized electronic fund transfer. That’s not just a security gap. It’s an examiner finding waiting to happen.
Why Transaction Monitoring Alone Is Not Enough
Most banks have built sophisticated fraud defenses at the wrong layer of the attack stack.
Transaction monitoring, MFA, behavioral analytics, and fraud scoring are all legitimate controls. But in fake-site ATO fraud, they share a critical flaw: they fire after the fake site has already done its job.
- Transaction monitoring fires too late. By the time a suspicious transfer triggers a rule, the fraudster already holds valid credentials. Experienced attackers deliberately mimic normal transaction patterns, moving funds in amounts and sequences that stay below detection thresholds until the loss is done.
- MFA is a speed bump, not a barrier. Modern phishing kits use real-time relay techniques, adversary-in-the-middle (AiTM) attacks, to capture OTP codes as customers enter them on a fake site and pass them to the legitimate bank site before they expire. As Krebs on Security reported in early 2026, services like Starkiller proxy the entire authentication flow in real time, meaning MFA “can be effectively neutralized despite functioning exactly as designed.” The CFPB’s own FAQ guidance explicitly notes that tricking consumers into providing texted account confirmation codes constitutes unauthorized access under Regulation E.
- Behavioral analytics and device fingerprinting operate on the fraudster’s session, not the customer’s. When a fraudster logs in with valid credentials from a new device, the behavioral signal is genuinely ambiguous. The result: false positives that slow investigation without preventing loss.
- Fraud scoring models struggle with novel attack vectors. They’re trained on historical patterns. A low-volume, targeted fake-site campaign against a specific customer segment can fly under the model’s radar entirely.
Financial institutions accounted for 18.3% of all phishing attacks in Q2 2025, the highest share of any sector, according to the APWG Phishing Activity Trends Report Q2 2025. That volume is hitting a control perimeter that doesn’t extend to where the attack actually begins.
Regulatory and Legal Risk Beyond Direct Reimbursement
Reimbursing a defrauded customer is the floor, not the ceiling, of your liability exposure. Compliance officers who treat Regulation E banking obligations as a pure accounting problem are missing three additional risk layers that can dwarf the direct reimbursement cost.
- CFPB supervisory scrutiny
The CFPB’s enforcement posture has shifted with the political winds in 2025, but the underlying statutory obligations under EFTA and Regulation E haven’t moved. Examination teams still assess whether institutions have adequate policies, procedures, and controls for unauthorized EFT claims, including whether investigation workflows are sound and whether provisional credit is being extended on schedule.
Banks with high volumes of fake-site fraud claims and thin investigation documentation are examination targets. As of January 2025, CFPB enforcement actions have resulted in $19.7 billion in consumer relief. That number signals what’s possible when the pendulum swings back.
- State-level consumer protection laws
Federal Regulation E sets the floor. States like California, New York, and Massachusetts layer stricter liability standards, shorter investigation timelines, and additional disclosure requirements on top of it.
State attorneys general have shown increasing appetite for digital banking fraud cases, particularly where large numbers of consumers are hit by the same attack campaign. In August 2025, New York Attorney General Letitia James sued Early Warning Services, the operator of Zelle, for failing to protect users from widespread fraud. When a single fraud campaign harms thousands of consumers, state regulators treat it as a systemic failure, not a series of individual incidents.
- Class action exposure
Fraudsters don’t deploy fake banking sites one at a time. A single phishing campaign can redirect thousands of customers to a cloned site within days. That scale creates exactly the conditions plaintiffs’ attorneys need to certify a class.
The Zelle fraud litigation provides the clearest precedent. Multiple class actions have argued that banks’ failure to implement adequate fraud prevention controls constitutes a breach of the duty of care owed to customers. The case Tristan v. Bank of America tested whether banks must reimburse customers deceived by scammers, and while the district court ruled for the bank, the case is now on appeal before the Ninth Circuit. The legal question isn’t settled. A single fake-site campaign affecting 5,000 customers creates a potential class with aggregate damages that no institution wants to defend.
- Reputational damage and customer churn
The financial hit doesn’t stop at legal fees and reimbursements. According to PYMNTS Intelligence’s ‘Financial Scams and Consumer Trust’ report (November 2025), 42% of scam victims consider switching banks after a fraud event, and 19% actually do. That’s nearly 10 percentage points above the general population’s bank-switching rate.
For a mid-size institution with 500,000 accounts, even a 1% increase in churn represents 5,000 lost customer relationships. Multiply that by average lifetime value and the reputational cost of a brand impersonation campaign quickly eclipses the direct reimbursement obligation.
Digital-native customers feel this most acutely. They have the lowest switching costs and the highest expectations for security. When they discover their bank’s brand was cloned and used against them, the trust damage is immediate and often permanent.
The Intersection of State Law and Federal Regulation E
Regulation E sets a federal floor, not a ceiling. States can impose stricter consumer protections on top of it, and several are doing exactly that.
For nationally operating banks, the practical implication is direct: your compliance exposure isn’t defined by the most lenient applicable standard. It’s defined by the most stringent one.
New York made that concrete in December 2025. Governor Hochul signed the Fostering Affordability and Integrity through Reasonable Business Practices (FAIR) Act into law, marking the first update to New York’s core consumer protection statute in 45 years. The FAIR Act expands prohibited conduct beyond “deceptive” acts to include “unfair” and “abusive” practices, and it substantially broadens the New York Attorney General’s enforcement authority. For banks with large New York customer bases, a fake-site fraud incident that triggers Regulation E disputes could simultaneously expose the institution to state-level enforcement action under a broader legal standard.
California’s Department of Financial Protection and Innovation (DFPI) has taken an equally aggressive posture, with active enforcement across digital financial services and a mandate to fill gaps where federal oversight recedes.
Here’s the kicker on documentation: state attorneys general hold subpoena authority. They can compel production of fraud investigation records, dispute resolution files, and internal communications. That makes your documentation practices a state-law compliance issue, not just a federal one. Banks that treat fraud records as internal housekeeping, rather than legally discoverable evidence, are carrying a risk they haven’t priced.
For compliance teams, the takeaway is direct: assess your fake-site fraud exposure against the strictest applicable state standard in your customer footprint, then build your controls and documentation practices to that bar.
What a Defensible Compliance Posture Looks Like in 2025
Here’s the question a senior examiner will ask your compliance committee: not whether fraud happened, but what controls you had in place before it did.
That framing matters. A defensible Regulation E banking posture in 2025 isn’t just about resolving claims correctly. It’s about demonstrating, with documentation, that your institution took reasonable steps to detect and disrupt the attack vector before customers were harmed. Here’s what that looks like across five operational areas.
- 1. Incident documentation requirements
For any Regulation E claim tied to fake-site or phishing-based credential theft, your investigation file needs to show more than a transaction log. Examiners will expect records of:
- The fraudulent site’s URL and the timeline of its deployment
- Evidence of how customers were directed to the fake site (phishing email, SEO poisoning, paid ads)
- The window during which the site was active and harvesting credentials
- The number of customers potentially exposed during that window
Without this documentation, you can’t conduct an adequate investigation, and you can’t defend your unauthorized EFT determination if it’s challenged. The documentation burden starts at detection, not at the claims desk.
- 2. Consumer notification obligations
When your institution becomes aware of a fake-site campaign targeting your customers, delayed notification isn’t just a reputational problem. It’s a compliance risk. Every hour a cloned site stays active is another window for credential submission, and another Regulation E claim in the pipeline.
Prompt notification, once a fake site is confirmed, limits the exposure window. It also demonstrates to examiners that your institution acted in good faith once the threat was identified.
- 3. Fraud investigation workflows
Fake-site fraud claims can’t run through a standard unauthorized EFT workflow. They require a distinct investigation path that includes:
- Cross-referencing the claimed fraud date against known fake-site activity windows
- Assessing whether the customer’s IP address or device fingerprint matches known attack infrastructure
- Documenting the specific basis for the unauthorized EFT determination, including why the transaction qualifies as unauthorized despite the customer initiating the login
Investigation teams without this workflow will either over-deny legitimate claims, creating regulatory exposure, or over-approve them without adequate documentation, creating audit risk.
- 4. Proactive detection controls as compliance evidence
This is where most banks have a gap, and where examiners are increasingly focused.
A bank that discovers a fake-site attack only after claims are filed is in a fundamentally weaker compliance position than one that detected and disrupted the attack in real time. The question examiners will ask is direct: what controls did you have in place to identify and respond to the fake site before customers were harmed?
As Frost & Sullivan noted in its 2025 Global Transformational Innovation Leadership Recognition for the FDP industry, enterprises find it increasingly difficult to protect against modern fraud attacks with reactive and traditional solutions. The recognition specifically cited Memcyco’s preemptive approach as the model for detecting and stopping fraud before it occurs.
Real-time fake-site detection and customer alerting is no longer just a security tool. It’s compliance evidence. It demonstrates that your institution had reasonable controls at the point where the deception actually begins.
- 5. Cross-functional escalation paths
Fake-site fraud sits at the intersection of fraud operations, compliance, and cybersecurity. Without defined escalation paths, each team waits for another to act, and the fake site stays live.
A defensible posture requires:
- Fraud teams receiving real-time alerts when a fake site is detected
- Compliance teams looped in automatically when a fake-site attack generates Regulation E claims
- Security teams authorized to initiate disruption actions without waiting for multi-department sign-off
The CISO of a top-10 North American bank described the operational impact of getting this right: incident handling times dropped from 72 hours to under one hour after deploying real-time detection capabilities.
That’s not just a security metric. It’s a compliance metric. Faster detection means fewer exposed customers, fewer claims, and a shorter documentation trail to defend.
Building the Investigation Documentation Framework
When a fake-site fraud claim lands on a compliance officer’s desk, the investigation is only as strong as the documentation behind it. Here’s what that file needs to contain.
- Per-claim documentation checklist:
- Date and time of alleged credential compromise
- URL and screenshot of the fake site, if available
- Evidence of how the customer was directed there: phishing email headers, SMS content, or search query records
- Timeline of fraudster activity after credential harvest (logins, transfers, account changes)
- Provisional credit issuance date and amount
- Investigation findings and the specific basis for the determination
- Consumer notification records, including method, date, and content
Every item on that list has a purpose. Examiners reviewing a disputed claim will look for the chain of evidence connecting the fake site to the unauthorized transfer. Gaps in that chain become gaps in your defense.
- Retention requirements: Under 12 CFR § 1005.13, financial institutions must retain compliance evidence for at least two years from the date an action is required. For fake-site fraud cases, that clock starts at the date of the claim. Every document in the checklist above must survive that window.
- The documentation gap real-time detection closes: Banks without fake-site detection are working blind. They can document what happened inside their systems after credentials were stolen, but they have no record of the attack itself: when the fake site went live, how many customers visited it, or what data was captured.
Banks that deploy real-time detection hold forensic data that changes the investigation entirely. That attack-side record supports determination findings, strengthens regulatory examination responses, and gives compliance teams something concrete to show examiners. It’s not just operationally useful. It’s compliance documentation that most banks currently can’t produce.
Real-Time Fake Site Detection as a Regulation E Compliance Control
The most effective Regulation E control isn’t a faster dispute resolution workflow. It’s stopping the fraud event before it starts.
Every fake banking site detected and disrupted before credentials are harvested can reduce the number of downstream fraud attempts, reimbursement events, investigations, and dispute files the institution has to manage. That’s the compliance logic behind treating real-time fake site detection as a first-line control, not a security add-on.
This is where Memcyco’s technology connects directly to the compliance framework.
- Preemptive infiltration: acting during the live attack window
Traditional takedown services operate on a report-and-respond model. A fake site gets flagged, a takedown request gets filed, and the site comes down, sometimes days or weeks later. During that window, customers keep arriving. Credentials keep getting harvested. Regulation E liability keeps accumulating.
Memcyco works differently. Memcyco’s Nano Defenders help surface signals from active impersonation attacks, enabling institutions to detect fake-site activity, identify affected users, and respond while the attack is still unfolding. As Frost & Sullivan’s analysis of Memcyco notes, this approach shifts protection upstream, reducing the exposure window before customers are compromised.
The practical compliance implication: disrupting fake-site activity before credential submission can reduce the number of downstream fraud claims, investigation files, and reimbursement decisions the institution has to manage. That’s not a security outcome. That’s a liability outcome.
- Individual victim identification: the compliance advantage most banks haven’t considered
Real-time detection identifies individual customers who visited the fake site, even before those customers file a dispute. This capability changes the compliance calculus in three ways:
- Proactive notification. Banks can alert at-risk customers immediately, reducing the window during which those customers remain unaware their credentials may be compromised. This directly shortens the exposure period that determines liability scope.
- Faster provisional credit decisions. When a customer files a Regulation E claim, the bank already holds documented evidence of fake-site exposure correlated to that customer’s account. The 10-business-day provisional credit clock starts with forensic data in hand, not a scramble to reconstruct the fraud chain.
- Stronger investigation documentation. Confirmed fake-site activity timestamps, matched to a customer’s claimed fraud date, are exactly the documentation that supports a defensible investigation record.
A CISO at a top-10 North American bank described the operational impact directly: “They took our incident handling times from 72 hours to less than 1 hour and saved us millions every month.”
- Agentless deployment: compliance controls that don’t require a 12-month IT project
One practical barrier to deploying new compliance controls is implementation overhead. Memcyco’s agentless model removes that barrier. There’s no end-user installation, no significant IT project, and no customer friction. The technology integrates into existing bank infrastructure and feeds detection data directly into SIEM systems and anti-fraud tools via API.
Fake-site detection data flowing into existing fraud investigation workflows means the cross-functional escalation paths that examiners expect, between fraud, compliance, and security teams, are supported by a single, correlated data stream.
- Quantified compliance ROI
Most compliance investments are framed as cost centers. Fake-site detection, measured against Regulation E liability exposure, looks different.
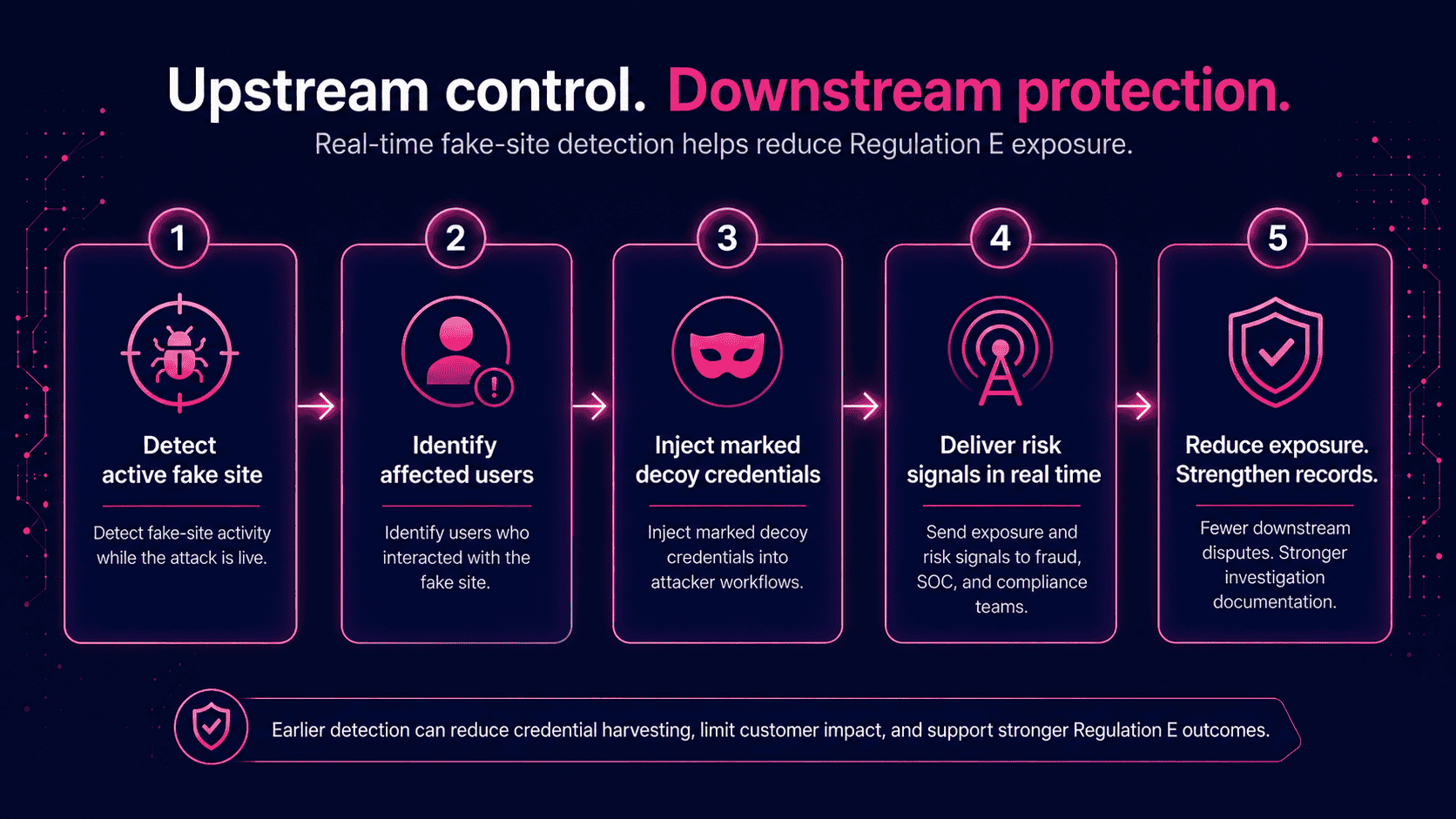
Memcyco’s documented customer outcomes provide a concrete framework:
- 50% reduction in ATO incidents directly reduces the volume of Regulation E claims filed
- Up to 90% reduction in investigation time cuts the operational cost of each claim that does get filed
- 10x ROI within the first year, reflecting reduced reimbursement costs, lower investigation overhead, and reduced regulatory exposure
David Mattei, Strategic Advisor at Datos Insights, put the compliance case plainly: “Memcyco’s technology provides financial institutions with visibility into fraud attempts before credentials are compromised, addressing a persistent blind spot in traditional security frameworks.”
That blind spot is exactly where Regulation E liability is accumulating. Closing it isn’t a cybersecurity decision. It’s a compliance decision.
From Takedown to Preemption: Why Timing Is the Compliance Variable
Here’s the question an examiner will ask when reviewing a fake-site fraud incident: when did the bank know, and what did it do next?
The answer exposes a compliance gap that most banks haven’t closed.
- The scan-and-takedown problem
Traditional brand monitoring runs on a discovery-then-removal cycle. A fake banking site goes live. Days pass. A customer complaint, a periodic scan, or a threat intelligence alert surfaces the site. A takedown request is submitted to the hosting provider or registrar. The site eventually comes down, typically 24-72 hours after discovery.
During that entire window, the site is live, harvesting credentials, and generating Regulation E exposure with every customer who lands on it. APWG recorded over one million phishing attacks in Q1 2025 alone, and research indicates the average phishing site operates for roughly 54 hours before removal. That’s 54 hours of unchecked liability accumulation.
- Preemption changes the compliance math
Memcyco takes a different approach. Rather than relying only on discovery and takedown, it helps detect fake-site activity while the attack is active, identify affected users, inject marked decoy credentials into attacker workflows, and generate evidence of impersonation exposure in real time.
The compliance impact is direct. Every hour a fake site remains active can increase the number of exposed users and downstream Regulation E claims. A bank that compresses the detection-to-response window from 72 hours to under one hour, as documented by Memcyco’s banking customers, is not just improving its security posture. It is reducing exposure, strengthening investigation readiness, and limiting the number of disputes that may follow.
- What examiners actually look for
A bank that discovers an attack through customer complaints, days after it began, is in a weak compliance position. A bank that can show real-time detection logs, immediate disruption actions, and individual victim identification is in a fundamentally stronger one. Timing isn’t a security metric here. It’s a compliance variable.
Action Checklist for Compliance and Fraud Teams
Most compliance audits reveal the same uncomfortable truth: controls are stacked at the back end of the fraud lifecycle, not the front. With account takeover fraud generating $15.6 billion in reported U.S. losses in 2024 and the FBI reporting $262 million in losses from financial institution impersonation schemes in 2025 alone, the window for reactive postures is closing fast. Use this checklist to identify where your exposure sits and what to fix first.
- 1. Audit current fraud controls for upstream coverage gaps
Map your existing controls against the full fake-site attack lifecycle. Identify the earliest point at which your stack can detect an active fake-site attack. If that point is after credential submission, you have an upstream gap that directly creates Regulation E exposure. Document it. That gap is your starting liability figure.
- 2. Review Regulation E dispute resolution workflows against updated CFPB guidance
Assess whether your investigators know to look for fake-site activity when a customer reports stolen credentials. Do your workflows prompt for fake-site forensic data? Can your team access that data? If the answer to either question is no, your dispute resolution process is incomplete under the updated guidance.
- 3. Assess documentation practices for impersonation-related fraud claims
Pull a sample of recent phishing or credential-theft Regulation E claims. Check whether investigation records include evidence about the fake site itself, not just the fraudulent transaction. Documentation that can’t demonstrate the basis for an unauthorized EFT determination won’t survive examiner scrutiny.
- 4. Evaluate real-time fake site detection as a compliance control
Determine whether your current brand protection or anti-phishing tools provide real-time detection and disruption, or whether they operate as scan-and-takedown services. The distinction matters: takedown services act after credential harvest has already begun. Assess whether your tools provide individual victim identification data that can feed directly into Regulation E investigation workflows.
- 5. Define escalation paths between fraud, compliance, and security teams
Document the escalation protocol for a confirmed fake-site attack: who is notified, in what timeframe, and with what authority to act. Compliance must be in the notification chain from the moment an attack is detected, not when Regulation E claims start arriving. If your current protocol routes fake-site alerts only to security, fix that now.
- 6. Review consumer notification procedures for fake-site attacks
Assess whether your procedures include proactive customer notification when a fake-site attack is live. Proactive notification reduces claim volume and signals good-faith compliance effort to examiners. It also shortens the window during which customers remain exposed.
- 7. Quantify your current fake-site fraud exposure
Pull Regulation E claims from the past 12 months that involved credential theft or account takeover. Estimate what percentage involved fake-site or phishing-based credential harvest. That figure is your baseline exposure. It’s also the number that makes the ROI case for upstream detection controls concrete and defensible to leadership.
Compliance teams that complete this audit often find the same gap: strong controls downstream, limited visibility upstream. Memcyco is built to help close that gap by detecting active fake-site attacks, identifying affected users in real time, injecting marked decoy credentials into attacker workflows, and delivering exposure signals that support faster fraud, security, and compliance response. Financial institutions using Memcyco have reported documented outcomes including a 50% reduction in ATO incidents and 10x ROI within the first year.
Key Takeaways
- 1. CFPB guidance makes clear that fraudulently obtained account access information can cause a subsequent covered EFT to qualify as unauthorized under Regulation E.
The ‘the customer authorized the login’ defense doesn’t hold when a fake site was the attack vector. Banks bear the liability, full stop.
- 2. The fraud chain begins at the fake site, not at the point of transfer.
Transaction monitoring, MFA, and behavioral analytics are necessary controls, but they all activate after the deception has already occurred. They can’t stop what they can’t see.
- 3. The full liability picture extends well beyond direct consumer reimbursement.
CFPB supervisory scrutiny, state consumer protection law exposure, class action risk, and customer churn mean the true cost of a fake-site fraud campaign runs 3-5x the direct reimbursement amount once all downstream costs are factored in.
- 4. A defensible compliance posture requires proactive detection controls, not just reactive investigation workflows.
Examiners will ask what controls were in place before the fraud occurred, not just how claims were handled after. Forensic documentation of fake-site attacks is now part of the compliance record.
- 5. Real-time fake-site detection can help reduce Regulation E exposure by disrupting credential harvesting before it creates downstream fraud claims.
Solutions that identify individual victims and generate attack forensics before credential submission don’t just improve security outcomes. They reduce claims volume, cut investigation costs, and shrink regulatory risk. That’s a compliance investment with quantifiable ROI.
The bottom line: fake-site detection is no longer optional for financial institutions managing Regulation E banking exposure. It’s the upstream control that every other fraud and compliance program depends on.
Conclusion
Regulation E banking liability for fake-site fraud isn’t a future risk. It’s current exposure. CFPB guidance makes clear that credentials obtained through deception can lead to unauthorized EFT claims when a fraudster uses them to initiate a covered transfer. Transaction monitoring catches fraud after the damage is done. The compliance gap closes when you stop the deception before credentials are submitted.
See How Memcyco Reduces Regulation E Exposure in Real Time
Memcyco helps financial institutions detect active fake-site attacks, identify affected users, and disrupt credential harvesting before it leads to downstream fraud claims. See how leading banks use Memcyco to reduce fraud exposure, shorten incident handling, and strengthen investigation workflows.
FAQs
Q: Are banks liable under Regulation E when a customer enters their credentials on a fake banking website?
A: Yes. Fake banking websites can create Regulation E exposure when fraudsters obtain account access information through deception and use it to initiate a covered EFT. The CFPB explicitly states that when a consumer is fraudulently induced into sharing account access information – including through fake websites – and a third party uses that information to initiate a transfer, the transfer is unauthorized. Banks cannot use the consumer’s act of entering credentials as a basis for denying the claim, because authorization obtained through deception does not constitute ‘actual authority’ under the statute.
Q: What is the difference between an ‘authorized’ and ‘unauthorized’ electronic fund transfer under Regulation E?
A: Under 15 U.S.C. § 1693a(12), an unauthorized EFT is one initiated by a person other than the consumer without actual authority to initiate the transfer, from which the consumer receives no benefit. The critical word is ‘actual authority’ – authority obtained through fraudulent misrepresentation (such as a fake banking site) does not qualify as actual authority. This means that even if a consumer physically typed their credentials, if those credentials were obtained through deception, the resulting transfer is unauthorized. The CFPB’s 2025 FAQ guidance reinforced this interpretation specifically in the context of phishing and fake-site attacks.
Q: What are a bank’s investigation obligations when a customer files a Regulation E claim related to fake-site fraud?
A: Under 12 CFR § 1005.11, financial institutions must: (1) investigate and determine whether an error occurred within 10 business days, with certain new-account transactions allowed up to 20 business days; (2) complete the investigation within 45 business days (90 days for POS transactions or foreign-initiated transfers); (3) provide a written explanation if the investigation determines no error occurred; and (4) maintain documentation of the investigation methodology and findings. For fake-site fraud claims, adequate investigation requires assessing whether a fake banking site was active during the claimed fraud period – which requires access to fake-site detection data that most banks currently lack.
Q: Can a bank deny a Regulation E claim if the consumer was negligent in clicking a phishing link?
A: No. Regulation E explicitly prohibits financial institutions from using consumer negligence as a basis for imposing greater liability than the statutory caps ($50 if reported within 2 business days, up to $500 if reported within 60 days). Even if a consumer clicked an obvious phishing link or failed to verify a website’s URL, the bank cannot use that negligence to deny the claim or shift liability beyond the statutory limits. The CFPB’s FAQ guidance reinforces that financial institutions cannot summarily deny unauthorized EFT claims based on the consumer’s role in the deception.
Q: Q: How does real-time fake site detection help reduce Regulation E exposure for financial institutions?
A: Real-time fake site detection helps reduce Regulation E exposure by preventing credential theft, supporting investigation documentation, and enabling faster customer notification. First, it detects and disrupts fake banking sites before more customers submit credentials, reducing the fraud events that can lead to Regulation E claims. Second, it generates evidence about fake-site activity, customer exposure, and related credential-risk signals, supporting stronger claims documentation. Third, it identifies affected customers, enabling proactive notification and faster response. Memcyco has documented outcomes including 50% reductions in ATO incidents and up to 90% reductions in investigation time at financial institution customers.
Q: What regulatory risks do banks face beyond direct consumer reimbursement under Regulation E?
A: Beyond direct reimbursement, banks face four additional risk dimensions from fake-site fraud: (1) CFPB supervisory scrutiny – examination teams assess whether banks have adequate policies, procedures, and controls for unauthorized EFT claims, and banks with inadequate fake-site fraud investigation documentation are examination targets; (2) State consumer protection law exposure – multiple states impose stricter liability standards than the federal Regulation E floor, and state attorneys general have shown increasing interest in digital banking fraud cases; (3) Class action litigation – when a fake-site campaign affects a large customer cohort, the conditions for class action are present, and plaintiffs’ attorneys have successfully argued that inadequate fraud prevention controls constitute a breach of the duty of care; and (4) Reputational damage and customer churn – customers who experience brand impersonation fraud lose trust in the institution, with PYMNTS Intelligence research identifying financial scams as a growing customer churn crisis for banks.
Q: What is the CFPB’s current position on bank liability for digital impersonation fraud?
A: CFPB guidance states that when a fraudster obtains a consumer’s account access information through fraud and uses it to initiate a covered EFT, the transfer can qualify as an unauthorized EFT under Regulation E. The Bureau specifically identifies phishing-based credential theft and fake-site attacks as scenarios that trigger unauthorized EFT protections. While the CFPB’s proposed interpretive rule extending EFTA to emerging payment mechanisms was withdrawn in May 2025, the FAQ guidance on stolen-credential EFTs reflects the Bureau’s longstanding interpretation of the existing statute and remains operative. Financial institutions cannot rely on previous commentary to summarily deny consumer claims of unauthorized EFTs in these scenarios.